Proposed Title :
FPGA Implementation of Block Interleaver with BPSK Modulation and Demodulation of Image Transmission and Reception
Improvement of this Project:
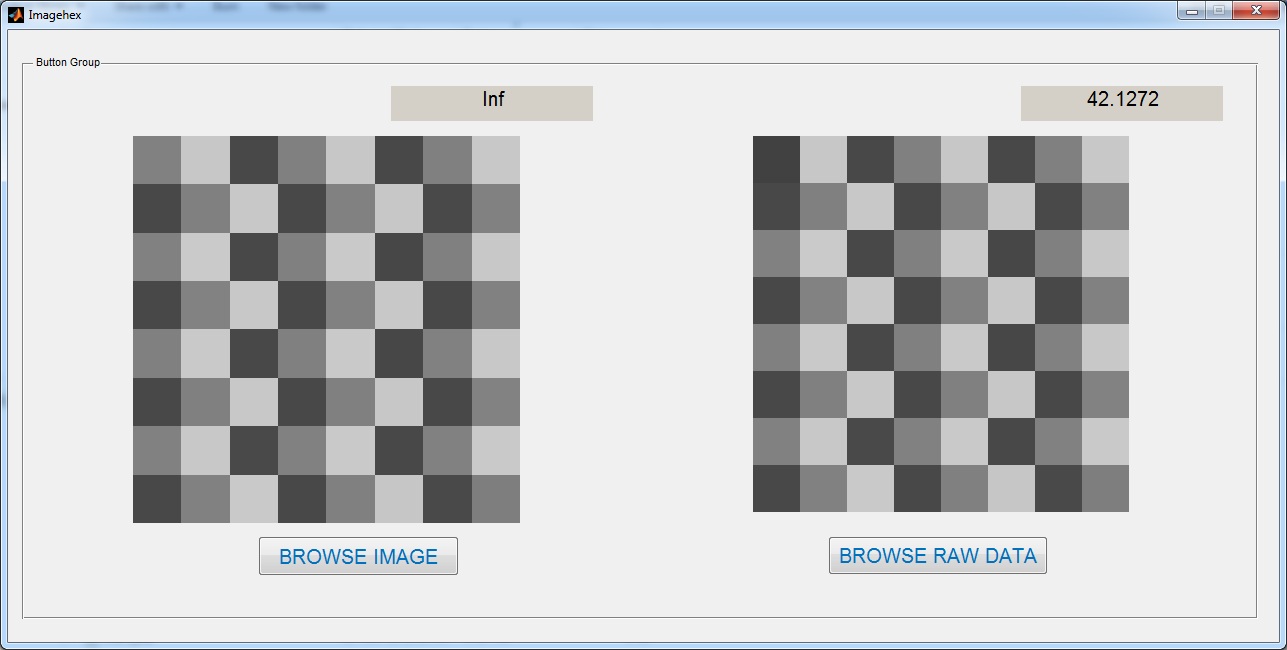
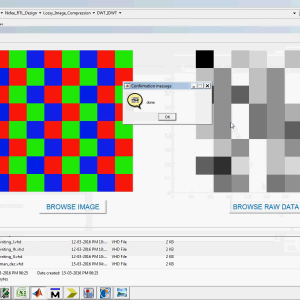
Design Interleaver and Deinterleaver with Image ( 8×8)
Low Power and Area Efficient
Software implementation:
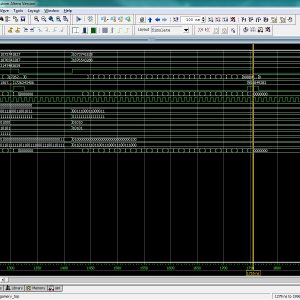
- Modelsim
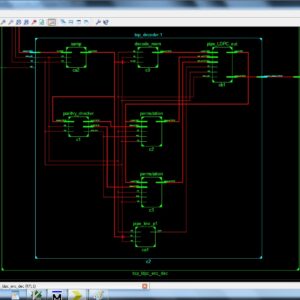
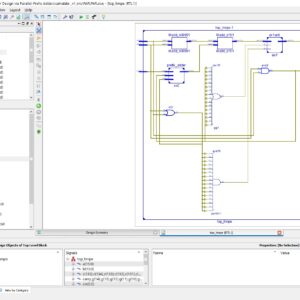
- Xilinx 14.2
Proposed System:
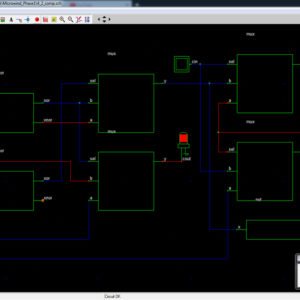
Interleaving is the process of rearranging the ordering of data sequence before transmission. Block interleaver is a popular interleaver employed in digital data transmission. It is simple and easy to implement whereas the other types of interleavers offer complexity in implementing. A block interleaver is in the form of a row-column matrix of size R*C; where R is total number of rows and C is the total number of columns. To perform interleaving, the information is written to the R*C row-column matrix row wise and read back in column wise as shown in Figure 1. There are no inter-row or inter-column permutations used in this illustration, thus the interleaved sequence holds some systematic order. The block deinterleaver performs the inverse operation of the interleaver in which the information is written to the R*C row-column matrix column wise and read back in row wise.
” Thanks for Visit this project Pages – Buy It Soon “
Block Interleaver Design for High Data Rate Wireless Networks
“Buy VLSI Projects On On-Line”
Terms & Conditions:
- Customer are advice to watch the project video file output, before the payment to test the requirement, correction will be applicable.
- After payment, if any correction in the Project is accepted, but requirement changes is applicable with updated charges based upon the requirement.
- After payment the student having doubts, correction, software error, hardware errors, coding doubts are accepted.
- Online support will not be given more than 3 times.
- On first time explanations we can provide completely with video file support, other 2 we can provide doubt clarifications only.
- If any Issue on Software license / System Error we can support and rectify that within end of the day.
- Extra Charges For duplicate bill copy. Bill must be paid in full, No part payment will be accepted.
- After payment, to must send the payment receipt to our email id.
- Powered by NXFEE INNOVATION, Pondicherry.
Payment Method :
- Pay Add to Cart Method on this Page
- Deposit Cash/Cheque on our a/c.
- Pay Google Pay/Phone Pay : +91 9789443203
- Send Cheque through courier
- Visit our office directly
- Pay using Paypal : Click here to get NXFEE-PayPal link



Reviews
There are no reviews yet.