Proposed Title :
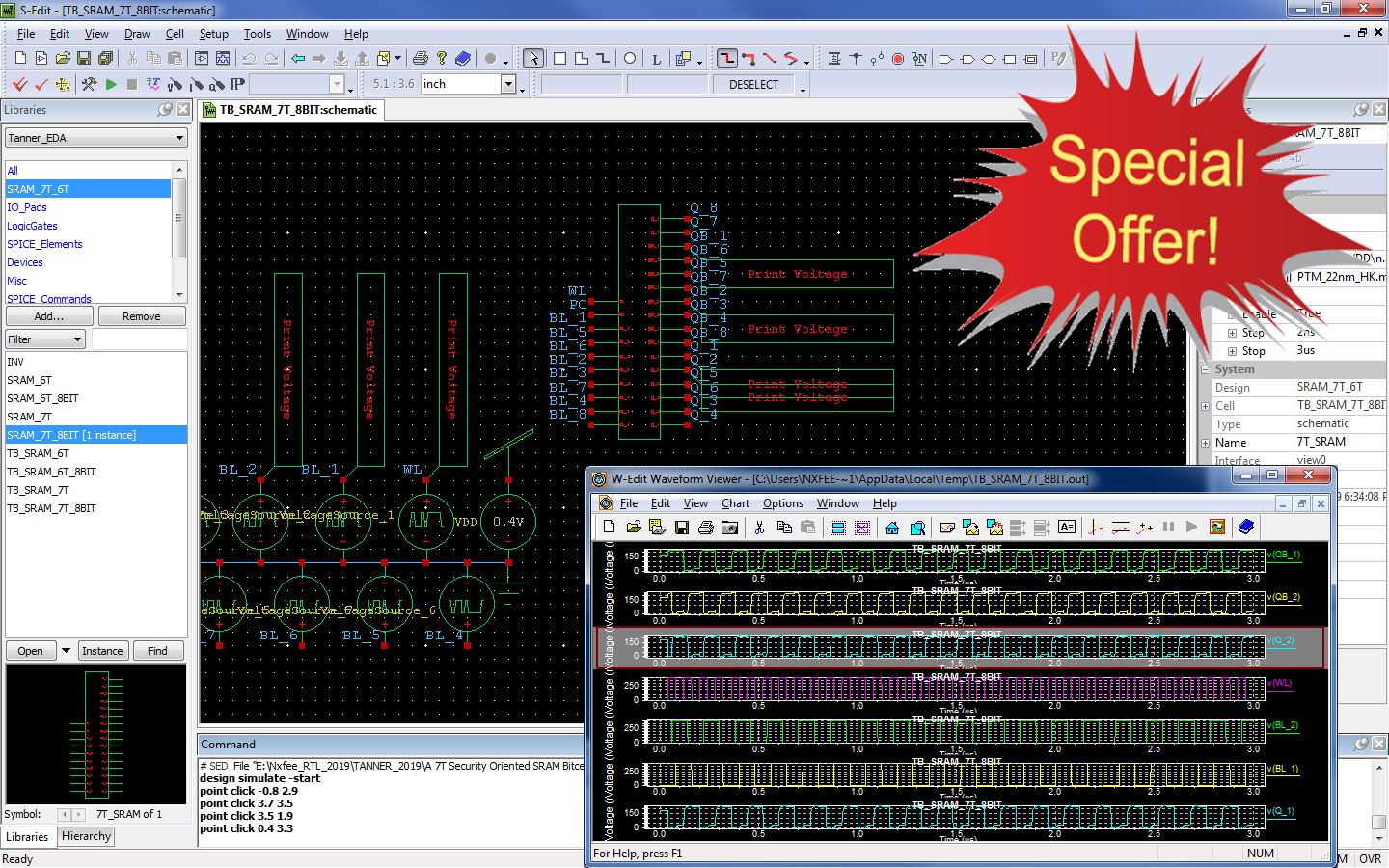
CMOS Implementation of Low Power and High Security Data Information using 7T SRAM Bit cell
Improvement of this Project:
To design a 7T SRAM bit cell in 22nm CMOS technology with single bit and 8-bit level operations with compared to existing 6T SRAM bit cell in terms of area, delay and power leakage.
Software implementation:
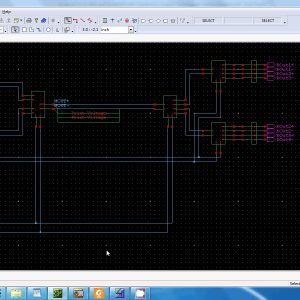
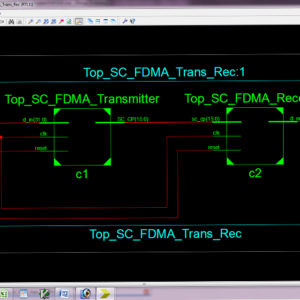
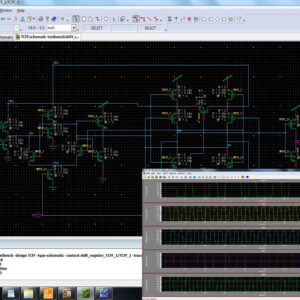
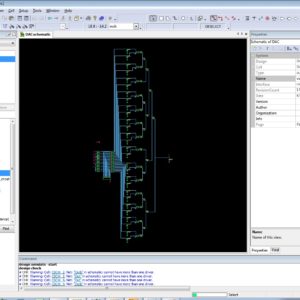
- TANNER EDA
Proposed System:
In recent method of Cryptographic application based devices which have more sensitive information with more crucial part of storing and retrieving the data. Thus its affect with power analysis and side channel analysis its exploit correlation between the instantaneous current consumed power supply devices with information leakages. In this work will describe a novel security oriented 7T SRAM cell design, which incorporates a two-phased write operations and significantly reduces the correlation between the written and stored data in the memory and its power dissipation, thus its providing a power analysis resilient memory. This proposed 7T cell includes an additional transistor to the existing 6T SRAM implementation with single power gate transistor per memory. Here, this proposed work will design a 7T SRAM bit cell in 22nm CMOS technology in TANNER EDA Software with single bit and 8-bit level operations with compared to existing 6T SRAM bit cell in terms of area, delay and power leakage.
” Thanks for Visit this project Pages – Buy It Soon “
A 7T Security Oriented SRAM Bitcell
“Buy VLSI Projects On On-Line”
Terms & Conditions:
- Customer are advice to watch the project video file output, before the payment to test the requirement, correction will be applicable.
- After payment, if any correction in the Project is accepted, but requirement changes is applicable with updated charges based upon the requirement.
- After payment the student having doubts, correction, software error, hardware errors, coding doubts are accepted.
- Online support will not be given more than 3 times.
- On first time explanations we can provide completely with video file support, other 2 we can provide doubt clarifications only.
- If any Issue on Software license / System Error we can support and rectify that within end of the day.
- Extra Charges For duplicate bill copy. Bill must be paid in full, No part payment will be accepted.
- After payment, to must send the payment receipt to our email id.
- Powered by NXFEE INNOVATION, Pondicherry.
Payment Method :
- Pay Add to Cart Method on this Page
- Deposit Cash/Cheque on our a/c.
- Pay Google Pay/Phone Pay : +91 9789443203
- Send Cheque through courier
- Visit our office directly
- Pay using Paypal : Click here to get NXFEE-PayPal link